I visited 33rd Chaos Communication Congress, which took place between 27th and 30th December 2016 in CCH in Hamburg. The motto of last year’s congress was Works for me. This was my fifth attendance of the Chaos Communication Congress.
The overall atmosphere on the Congress and organization was excellent as always. However, I have to admit that the quallity of talks was worse when compared to previous years. During previous Congresses I had problems with choosing which talk to attend as there were too many of them I wanted to visit at the same time. 33C3 was different. I was kind of bored on 3rd and 4th day. Also, there were huge problems with tickets as I was able to get a ticket only in the last sale round. With such a huge interest in the Congress I thought there was going to be a lot more people when compared to previous years, but this wasn’t the case. 32C3 was much more crowded than 33C3 was (I am not complaining, but I expected a lot more people)!
I have visited the following talks:
Day 1
-
The Figth for Encryption in 2016 (Video) - Kurt Opsahl from EFF gave the summary of 2016 development in the crypto ecosystem. 2016 was a year in which end-to-end encryption was deployed in all major messengers as well as attempts to weaken crypto by governments.
-
Bootstrapping a slightly more secure laptop (Video) - Trammel Hudson spoke about his work on Heads, which is a custom secure opensource firmware for laptops and servers that want to provide a much better physical security. It is based on the Linux Kernel and Coreboot. I liked this talk very much.
-
Law Enforcement Are Hacking the Planet (Video) - this talk was about how FBI uses exploits and the speaker spoke about Operation PACIFIER and Torpedo. The operation covered the takedown of child pornography Tor hidden service and how FBI uses malware to discover site’s visitors.
-
Shut up and Take My Money! (Video) - this talk was a hillarious one! It describes N26 Internet bank security issues. It is really worth watching this video. If you are a software developer and you want to learn how to write secure applications, it is a must watch.
-
Geolocation methods in mobile networks (Video Slides) - a good overview of various geolocation techniques in mobile networks. The talk might seem little boring, but there are a few new ideas presented as well.
-
Untrusting the CPU (Video) - this talk describes a proposal for a more secure CPU architecture. The idea is to move as much sensitive data as possible out of present-day CPUs. I left this talk after some time for late lunch.
-
Deploying TLS 1.3: the great, the good and the bad (Video) - a talk by Filippo Valsorda and Nick Sullivan (both from Cloudflare) about the next generation of TLS. TLS 1.3 removes insecure ciphers and broken parts of older TLS versions (e.g. TLS compression), introduces new cryptographic ciphers (ChaCha20-Poly1305), digital signature algorithms (Ed25519 and Ed448), key exchange protocols (x25519 and x448), integrates use of session hash and increases performance (1-RTT handshake and initial support for 0-RTT). TLS 1.3 is still a draft and should be ready around February 2017. This talk is a must watch for everybody who deals with web application infrastructure!
-
You can -j REJECT but you can not hide: Global scanning of the IPv6 Internet (Video) - summarizes and shows how to use various scanning techniques to discover live hosts in IPv6 networks. Speaker also showed visualization of big IPv6 networks e.g. .mil. I liked this talk and it is definitely a must watch for people interested in networking and security.
Day 2
-
Syrian Archive (Video) - a group of people who try to document and validate what is happening in Syrian Civil War conflict zones. They developed a tool which preserves video evidence and workflow to verify video footage.
-
Gone in 60 Milliseconds (Video) - one of the best talks on 33c3. The speaker talked about attacking AWS Lambda-based applications which don’t run longer than few milliseconds. Even though the application runs for few milliseconds, it can still be attacked by using and leveraging cloud provider’s other technologies. I especially liked the way how he presented the talk. This is a must for anyone working with AWS Lambda!
-
Recount 2016: An Uninvited Security Audit of the U. S. Presidential Election (Video) - Matt Bernhard and J. Alex Halderman talked about events after the U. S. presidential elections. They showed that the voting machines are very easy to hack and that somebody could have manipulated the vote easily. They also described what happened to the presidential election recounts, how they ended and what should be changed so that future U. S. elections are secure. They also showcased how crazy voting recount laws in some U.S. states are. If you are interested if the elections were hacked, check out this video.
-
The Untold Story of Edward Snowden’s Escape from Hong Kong (Video) - this talk sheds light on what happened during 2 weeks between the moment Edward Snowden left the hotel in Hong Kong and his landing in Moscow. This talk also tells the stories of people who helped Edward Snowden and what we can do for them. In the beginning of this talk, there were some technical problems, so you can skip first 10 or 15 minutes.
-
State of Internet Censorship 2016 (Slides) - this talk summarizes year 2016 in Internet censorship landscape. It contains information about threats and trends in this area as well.
-
Intercoms Hacking (Video) - ever wondered how to hack intercoms? In the past, Intercoms were connected by wires, but trends and technologies used are changing. This talk will give you a nice intro to the topic and how to approach the problem. This talk was wonderful and I enjoyed it.
-
ATMs how to break them to stop the fraud (Video) - various ways how ATMs can be hacked, what can be done to prevent ATM hacking and nice overview of the problems.
Day 3
-
Dissecting modern (3G/4G) cellular modems (Video Slides) - this talk provides a detailed look at some modern 3G/4G cellular modems and what can be found out about their internals using debug interfaces and various hacking techniques. Speakers were also talking about how they reverse engineered cellular modems and showed what they were able to achieve with hacked cellular modems.
-
The Moon and European Space Exploration (Video) - The second talk in Space track. Jan Wörner spoke about the European Space Agency, its purpose, how they work and what they are working on. He also gave details about The Moon Village. I enjoyed this talk very much.
-
Interplanetary Colonization (Video) - Liz George and Peter Buschkamp spoke about travelling in space, colonization of other planets and gave more insight into the problems we as the species are facing on this front.
-
Lasers in the sky (with asteroids) (Video) - Peter Buschkamp spoke about space and airborne lasers and their practical uses.
Day 4
-
Retail Surveillance / Retail Countersurveillance (Video) - this talk surveys current and emerging trends and technologies used in retail surveillance. Adam Harvey also spoke about face recognition and what can be gathered from such analysis.
-
Understanding the Snooper’s Charter (Video Slides) - the talk analyzes the Investigatory Powers Act aka Snooper’s Charter in the UK, what it means for everybody and how it affects everyday life. With this law in place, the UK became unnoticable surveillance state.
-
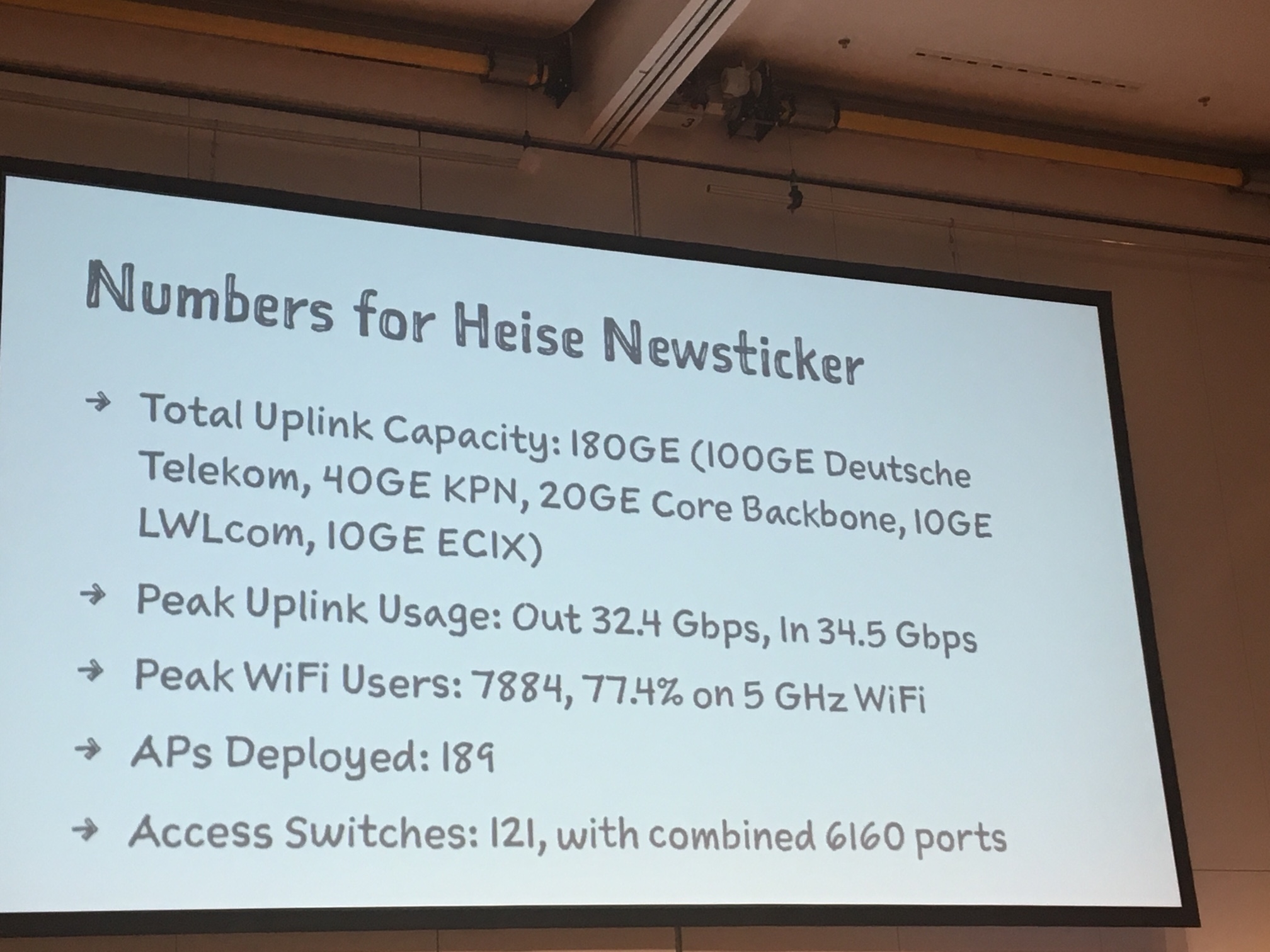
33C3 Infrastructure Review (Video) - the most awaited and the most interesting talk of the day. This talk gives an overview of metrics, numbers and other aspects of the Congress. The most interesting facts were related to networking and they are shown on the picture below:
Talks I haven’t visited, but are interesting:
- What could possibly go wrong with <insert x86 instruction here>? (Video Slides)
- How Do I Crack Satellite and Cable Pay TV? (Video)
- 3 Years After Snowden: Is Germany fighting State Surveillance?
- On Smart Cities, Smart Energy, And Dumb Security
- Tapping into the core (Video)
- On the Security and Privacy of Modern Single Sign-On in the Web (Video Slides)
- Virtual Secure Boot (Video)
Other interesting links:
To conclude, I enjoyed 33C3 very much and I am looking forward for 34C3. See you there!