This blog post will summarize my experience attending 35th Chaos Communication Congress AKA 35c3, which took place between 27th and 30th December 2018 in Leipzig, Germany. The Congress hosts a variety of talks, assemblies and serves as a meeting point for thousands of people from the security and hackerspace communities. Moreover, the Congress covers many other different topics ranging from arts & culture, technology, hobby projects as well as politics. In this post, I will be mainly focusing on the security and technical talks of the conference.




Mobility
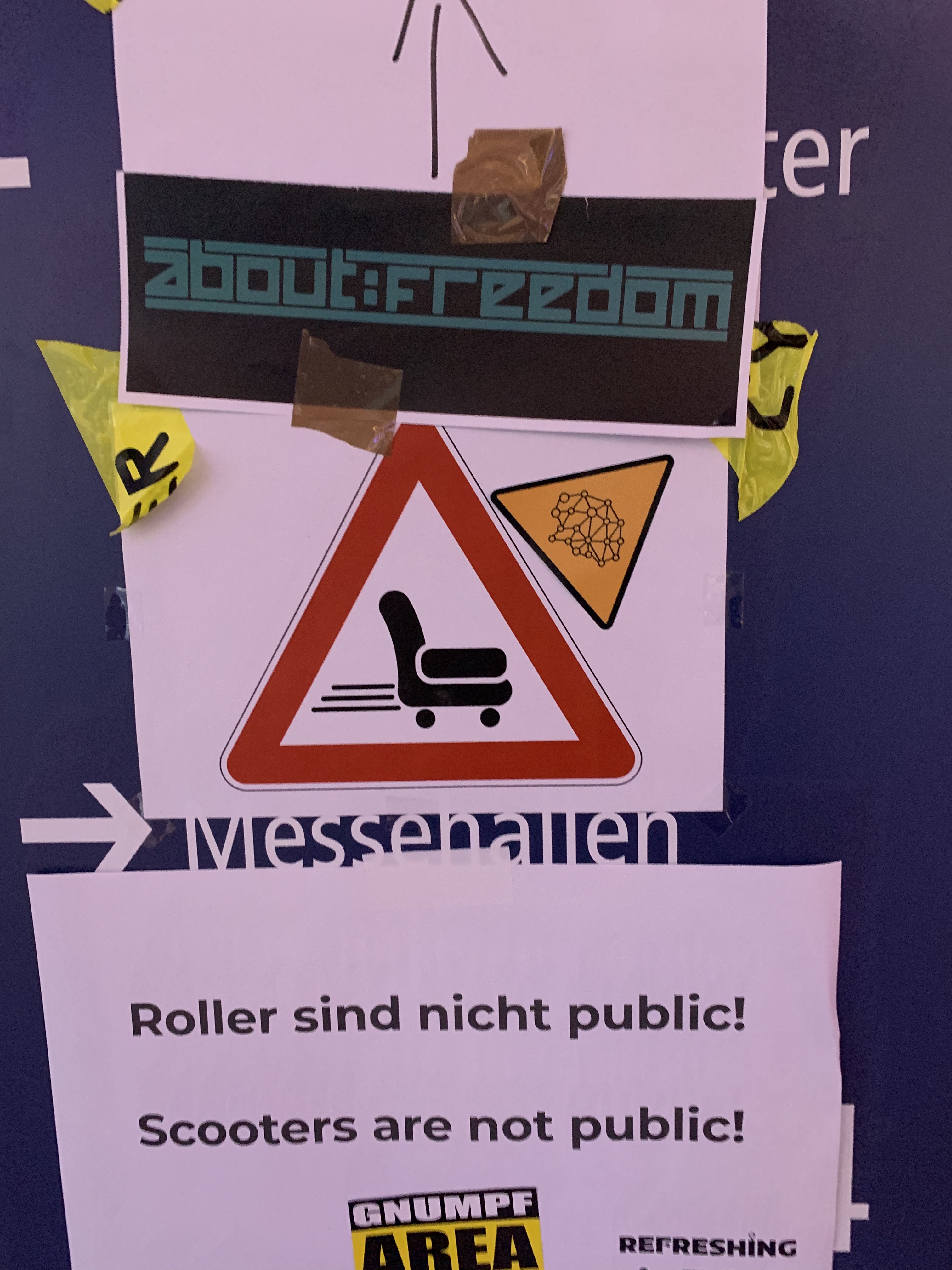
Given the size of the CCL, a lot of people were using scooters, both eletrical and mechanical, as well as special tailor-made mobile vechiles.
As some of the mobile vechiles were actually causing traffic problems, traffic warning signs were put up around the Congress. In addition, not many attendees realized that scooters were as a matter of fact not free-for-all and were owned by participants.
Oh, and let’s not forget the racing track!

Talks
I went along to the following talks:
Day 1
-
The Rocky Road to TLS 1.3 and better Internet Encryption (Video Slides) - this talk gives a detailed overview of TLS 1.3, hilighting reasons for decisions that were made in the design of the new TLS version and how it differs from TLS 1.2 as well as talks about deployment peculiarities.
-
First Sednit UEFI Rootkit Unveiled (Video Slides) - researcher presents a detailed analysis of the first UEFI rootkit spotted in the wild and talks about how it works internally.
-
SiliVaccine: North Korea’s Weapon of Mass Detection (Video) - overview of the antivirus software created by comrades in North Korea and how software engineering problems are handled.
-
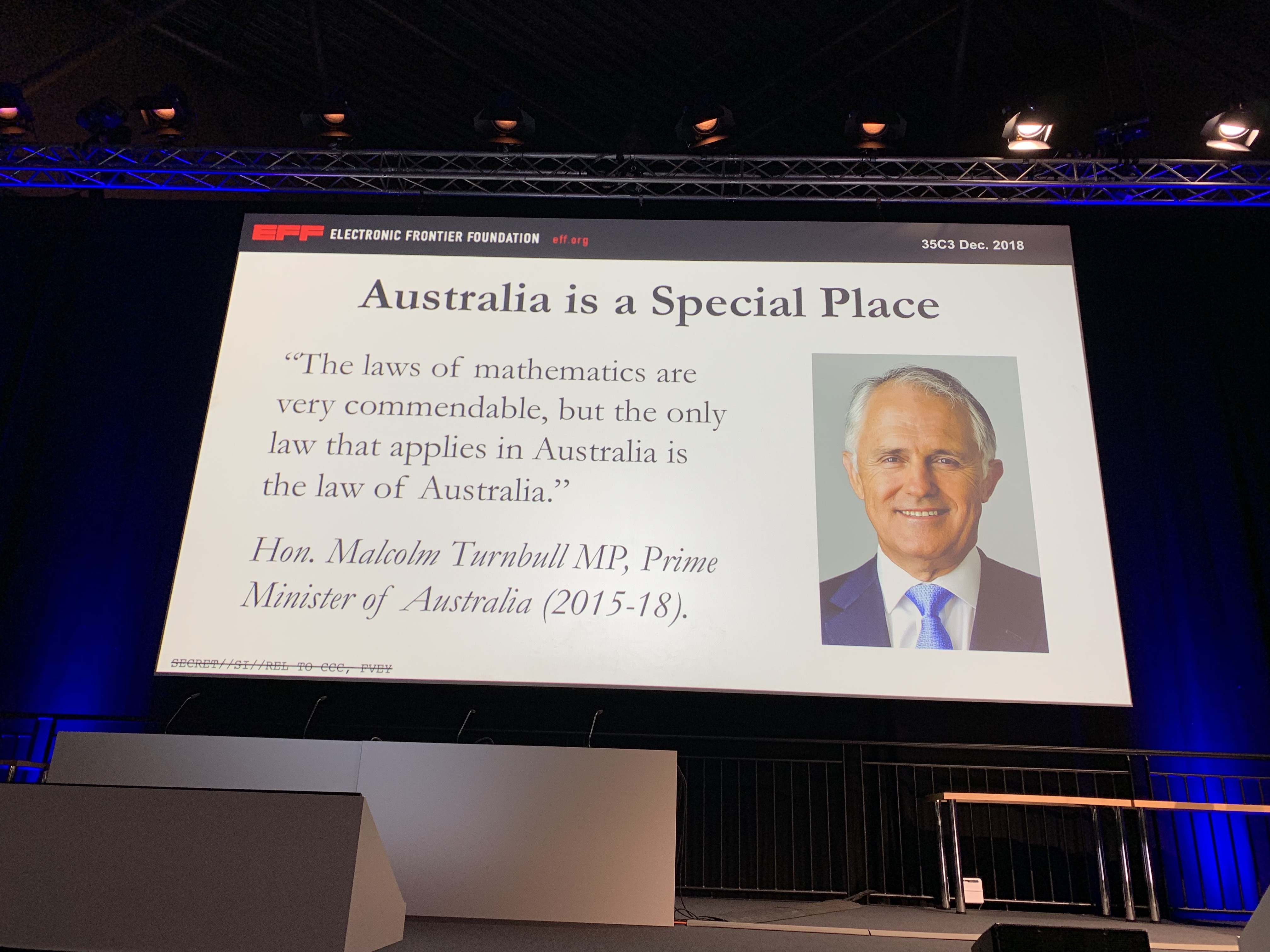
It Always Feels Like the Five Eyes Are Watching You (Video) - EFF’s Kurt Opsahl speaks about the espionage alliance between Australia, Canada, New Zealand, the United Kingdom and the United States, it’s past and present and what are they doing in order to enable mass surveillance.
Day 2
-
Jailbreaking iOS (Video) - talk gives a general overview how iOS jailbreaking works, describing past techniques and how newer iOS protections are making it more complicated. A few jailbreaking pieces of software were also described.
-
The year in post-quantum crypto (Video Slides) - traditional talk one cannot miss out on! Speakers, Daniel J. Bernstein and Tanja Lange, summarize the development during the last year in post-quantum cryptography space ranging from events that appeared in the news to PQ cipher analysis.
Day 3
-
Enclosure-PUF (Video) - ever wondered how to design a tamper-proof physical case for computers? This talk will give you an insight on how to use electromagnetic waves for this exact purpose. Speakers also talk about the design and issues of such solution.
-
Sneaking In Network Security (Video) - summary of how Airbnb tackled and deployed network segmentation into their infrastructure, what problems they ran into and how one should approach the whole problem.
-
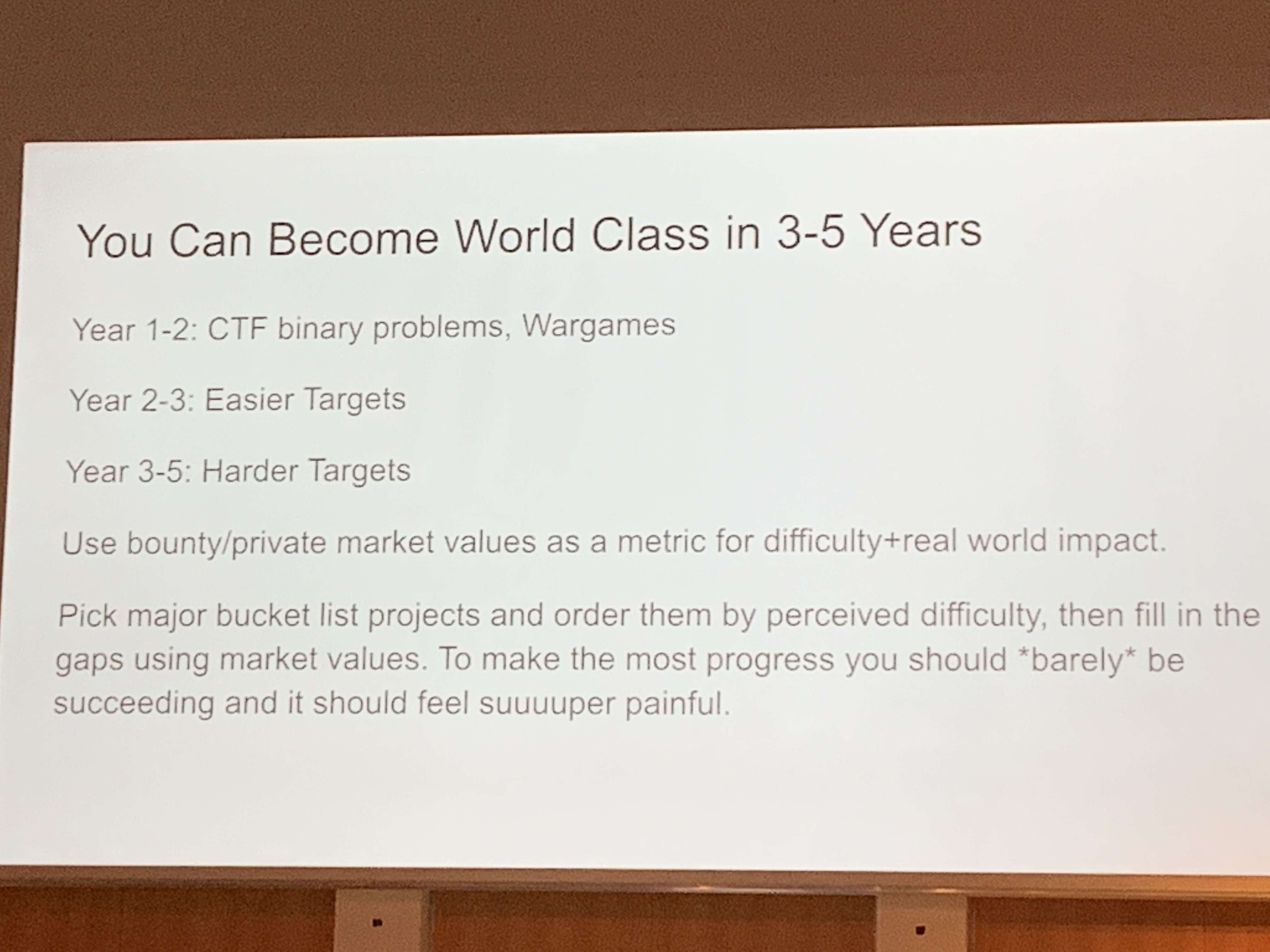
Attacking Chrome IPC (Video) - this talk unveils techniques on how to become proficient in bug hunting as well as talking about how the speaker was able to apply these methods in finding vulnerabilities in Chrome IPC. Definitely a must watch for somebody who is interested in becoming a security researcher!
-
Internet of Dongs (Video) - one of my most favourite talks at the Congress this year! The speaker talks about how smart sex toys were researched, what kind of bugs and issues were found and how by misuse of these tools one might commit a criminal activity.
-
The foodsaving grassroots movement (Video Slides) - this talk introduces the foodsharing movement, whose aim is to reduce the food waste and what people can do to help. This one was quite inspiring!
Day 4
I skipped Day 4 as my flight was scheduled early in the morning. However, here are some talks that I find of great interest and I would have visited them if I was still at the Congress on Day 4:
- Kernel Tracing With eBPF (Video Slides)
- Dissecting Broadcom Bluetooth (Video Slides)
- 35C3 Infrastructure Review(Video)
Other talks
Talks I haven’t frequented, but sounded interesting:
- Hunting the Sigfox: Wireless IoT Network Security (Video)
- wallet.fail (Video)
- Compromising online accounts by cracking voicemail systems (Video Slides)
- What The Fax?! (Video )
- Modchips of the State (Video)
- Inside the AMD Microcode ROM (Video) Slides)
- SD-WAN a New Hop (Video Slides)
- Exploring fraud in telephony networks (Video)
- Modern Windows Userspace Exploitation (Video)
- Smart Home - Smart Hack (Video)
- Analyze the Facebook algorithm and reclaim data sovereignty (Video)
- Attacking end-to-end email encryption (Video)
- Wallet Security (Video Slides)
- A Christmas Carol - The Spectres of the Past, Present, and Future (Video)
- The Layman’s Guide to Zero-Day Engineering (Video)
- From Zero to Zero Day (Video)
- Provable Security (Video Slides)
- Viva la Vita Vida (Video)
- In Soviet Russia Smart Card Hacks You (Video Slides)
- Memsad (Video)
- Web-based Cryptojacking in the Wild (Video Slides)
- Circumventing video identification using augmented reality (Video)
Other interesting links:
- Fahrplan (35c3 schedule)
- 35C3 videos on media.ccc.de
- 34C3 EN video playlist on YouTube
- 35C3 FR video playlist on YouTube
- 35C3 ES video playlist on YouTube
- 35C3 DE video playlist on YouTube
To conclude, I enjoyed 35C3 very much and I am looking forward to 36C3. See you there!