New location AKA Willkommen in Leipzig
My first visit to 29C3 in 2012 was the year when Congress moved from Berlin to Hamburg. Bigger auditoriums, more room for more people. After the last year’s problems with almost 2000 people not getting to 33C3 because of the congress hall capacity limits, CCC organizers decided to look for a new venue. They found one in the city of Leipzig and Congress Hall Leipzig.

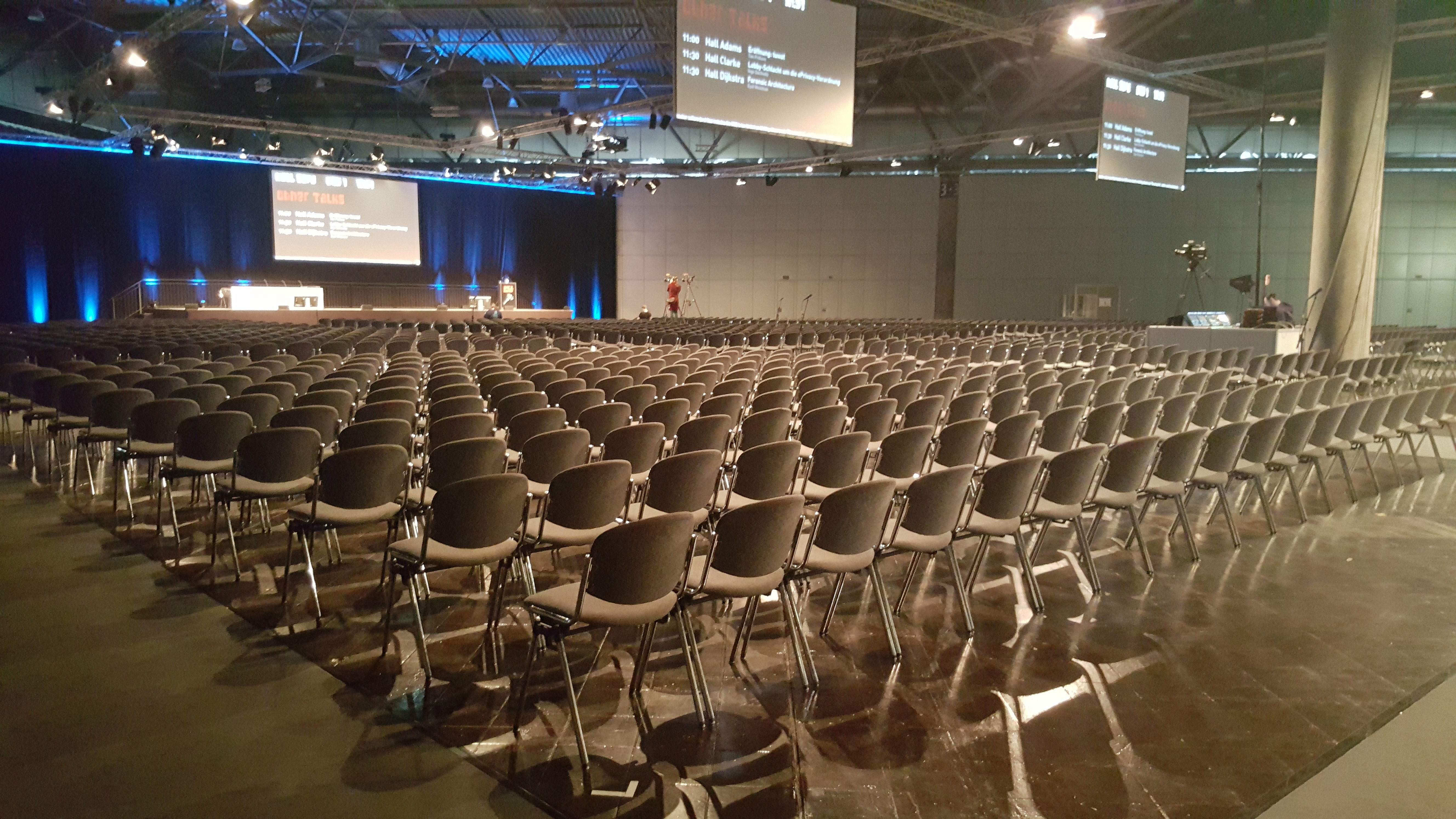
The venue is way bigger than CCH was. It even felt way bigger. It was extremely spacious, it takes around 5 minut to move between auditoriums. When compared to CCH, assembly space was 3 times bigger. However, one downside when compared to CCH is the CCL’s location - on the outskirts of Leipzig. It took me around 20 minutes to reach the venue from my hotel. However, the transportation was planned quite well as CCC organizers were able to give out special Zone 101 tickets for the public transport. There was also a special tram line going every 5-10 minutes between CCL and the city centre.

34C3 motto was tuwat (“do something”). More on the context can be found in this video.
Talks
34C3 was focused on plethora of topics covering IT security, technology, privacy as well as politics. I have visited the following talks:
Day 1
-
Demystifying networks cards (Video Slides) - this talk gave a brief overview of how do network cards and operating systems interacts together as well as various new approaches for boosting performance.
-
Uncovering British spies’ web of sockpuppet social media personas (Video) - overview of GCHQ activies on social media creating fake content and focus on how GCHQ tried to infiltrate activist groups around the world.
-
Squeezing a key through a carry bit (Video Slides) - Filippo Valsorda talked and explained a security vulnerability in Go implementation of P-256 due to misplaced carry bit. He also showed us a Holywood-ready tooling he worked on. I enjoyed this talk a lot.
-
Unleash your smart-home devices: Vacuum Cleaning Robot Hacking (Video Slides) - a talk about a design, inner working and how to rooting robotic vacuum cleaners. Very funny topic indeed.
-
Inside Intel Management Engine (Video) - overview of Intel Management Engine and a vulnerability, which allows ME debugging.
-
Defeating (Not)Petya’s Cryptography (Video) - this talk gives information about Petya cryptography flaws and how the speaker was able to them and decrypt infected computers.
-
KRACKing WPA2 by Forcing Nonce Reuse (Video Slides) - very detailed look at KRACK attack on WPA2 wireless networks.
Day 2
-
Mobile Data Interception from the Interconnection Link (Video) - overview of Diameter and LTE networks as well as how data interception can be achieved via the Diameter-based interconnection link.
-
Spy vs. Spy: A Modern Study Of Microphone Bugs Operation And Detection (Video Slides) - overview of various microphone bugs, their way of operation and detection. I expected more from this talk.
-
Intel ME: Myths and reality (Video Slides) - speaker gives a detailed look at Intel ME, it’s functionality, myths and things they discovered while reverse engineering Intel ME firmware. One of the best talks in the whole Congress, I enjoyed it quite a lot.
-
LatticeHacks (Video) - a talk describing what Lattices are, how they affect cryptography and cryptanalysis. This was a joint presentation by Daniel J. Bernstein, Nadia Heninger, and Tanja Lange. I liked this talk a lot as well.
Day 3
-
Taxation (Video) - overview of how tax evasion works and what can be done with it.
-
Bringing Linux back to server boot ROMs with NERF and Heads (Video) - Trammel Hudson spoke about his NERF and HEADS project, how to replace propietary BIOS on server motherboards with Linux and the general concept.
-
Internet censorship in the Catalan referendum (Video Slides) - this talk describes the events and actions taken by Spain in the days before the Catalan referendum on independence, points out how the censorship happened and what activists did to bypass it.
-
Protecting Your Privacy at the Border (Video) - talk by EFF on how to protect your privacy when carrying your laptop or mobile device through the border crossing.
Day 4
I skipped Day 4 as my flight was scheduled in the morning. However, some talks I was interested in:
Talks I haven’t visited, but I found interesting:
- iOS kernel exploitation archaeology (Video)
- Lets break modern binary code obfuscation ([Video][https://media.ccc.de/v/34c3-8789-lets_break_modern_binary_code_obfuscation] Slides)
- BootStomp: On the Security of Bootloaders in Mobile Devices (Video)
- Microarchitectural Attacks on Trusted Execution Environments (Video)
- DPRK Consumer Technology (Video)
- Doping your Fitbit (Video Slides)
- BGP and the Rule of Custom (Video Slides)
- Practical Mix Network Design (Video Slides)
- We should share our secrets (Video Slides)
- Deep Learning Blindspots (Video)
- Reverse engineering FPGAs (Video)
- May contain DTraces of FreeBSD (Video)
- Internet of Fails (Video Slides)
- Everything you want to know about x86 microcode, but might have been afraid to ask (Video Slides)
- ASLR on the line (Video Slides)
- History and implications of DRM (Video)
- OONI: Let’s Fight Internet Censorship, Together! (Video)
- avatar² (Video Slides)
- Decoding Contactless (Card) Payments (Video)
- Hardening Open Source Development (Video)
Other interesting links:
- Fahrplan (3333 schedule)
- 34C3 videos on media.ccc.de
- 34C3 EN video playlist on YouTube
- 34C3 DE video playlist on Youtube
- 34C3 ES video playlist on Youtube
To conclude, I enjoyed 34C3 very much and I am looking forward for 35C3. See you there!